Latest Blog
The Invisible Threat: How to Spot (and Stop) Hiring Fraud in a Remote-First World
Researcher
•
5 min read
Share this post
The Invisible Threat: How to Spot (and Stop) Hiring Fraud in a Remote-First World
There was a time when "hiring fraud" felt like a plot point from a corporate thriller—something that happened to other companies, usually in high-stakes finance or government roles.
But the shift to remote-first work and the explosion of generative AI have changed the math. Today, hiring fraud is a high-volume, low-effort game for bad actors. From "proxy interviewers" who ace the technical round for someone else, to candidates using real-time AI tools to script their answers, the modern hiring funnel is under siege.
The goal isn't to turn your recruiters into private investigators. The goal is to build a fraud-resistant process that protects your company without alienating the great candidates you actually want to hire.
Here is how to spot the red flags before you send the offer letter.
The Three Pillars of Candidate Integrity
Most hiring teams focus exclusively on Capability (can they do the job?). Fraudsters exploit this by ignoring Identity and Intent. To protect your funnel, you need to verify all three:
Identity: Are they who they say they are?
Capability: Can they do the work live, without hidden assistance?
Intent: Are they looking for a career, or looking for unauthorized access to your data and systems?
1. Catching Red Flags at the Top of the Funnel
Fraud detection starts at the application stage. You aren't looking for "proof" here; you’re looking for inconsistency. One mistake is a typo; three mistakes are a pattern.
The "Constructed" Profile: Be wary of LinkedIn profiles created within the last six months with fewer than 50 connections and no credible "overlap" with known industry peers.
The Generic Resume: Does the work history list specific outcomes and constraints, or does it read like a copy-paste of a job description? Fake candidates often use "buzzword soup" to bypass ATS filters but struggle to name specific tools or team structures.
The Triangulation Test: Does the name on the resume match the email, the LinkedIn URL, and the portfolio? If they claim to be in New York but their metadata or time zone availability suggests otherwise, it’s time to dig deeper.
2. Exposing the "Proxy" During the Screen
The initial recruiter screen is where most proxy interviewing happens—where one person does the talking to get the "candidate" to the next round.
The "Technical Difficulty" Loop: Frequent camera "malfunctions" or audio delays during identity verification or ownership questions are classic stalling tactics.
Unnatural Pauses: If a candidate takes five seconds to answer a simple question about their own resume, they might be waiting for a prompt from a tool or a person off-camera.
The Ownership Deep-Dive: Ask: "What was a specific trade-off you made on this project?" Proxies can memorize a project's "what," but they usually fail the "why."
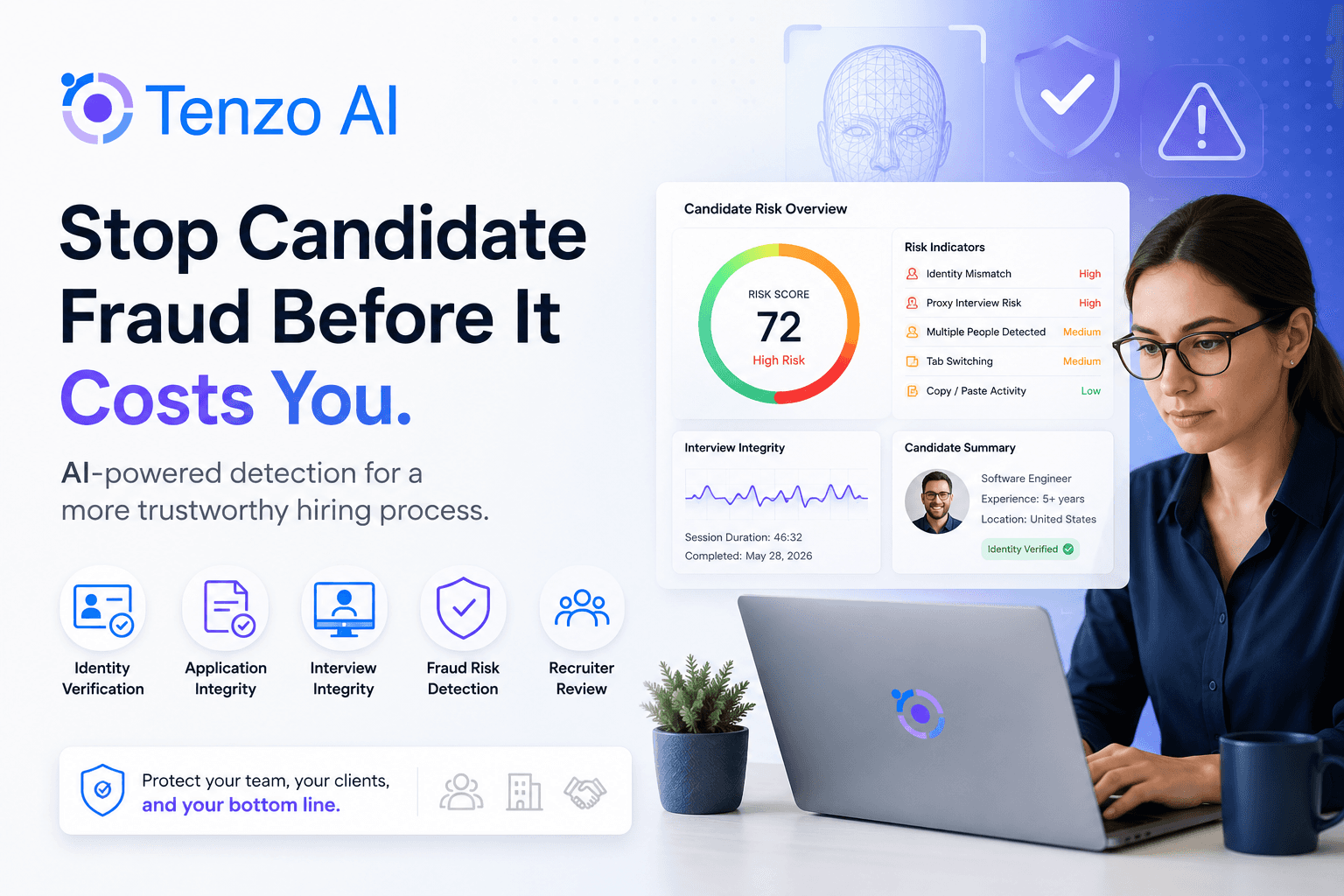
Where Tenzo comes in: Manually checking every candidate's location and identity is a massive time-sink. Tenzo standardizes these screens, adding lightweight, automated identity and presence checks into the flow. It ensures every candidate is verified using the same objective criteria, so your recruiters can focus on the conversation, not the paperwork.
3. Interviewing in the Age of AI
With tools like ChatGPT and Cluely, "searchable" interview questions are officially dead. If a candidate can Google the answer or prompt an AI for it, the signal is zero.
The "Explain + Extend" Model
The best way to verify work is to make the candidate live with it. If you use a take-home assignment or a portfolio review, don't just let them present it.
Explain: Give them 5 minutes to walk through a specific decision.
Extend: Change the constraints. "What if the user base doubled overnight?" or "How would you rewrite this if we couldn't use [Tool X]?"
People who did the work can adapt on the fly. Those who didn't will hit a wall.
4. The Offer Stage: Closing the Security Loop
Fraud isn't always about a "fake" person; sometimes it’s a real person with a fraudulent intent, like "job double-dipping" or data theft.
Logistics Friction: Be wary if a candidate pushes back on shipping equipment to a verified address or tries to bypass standard background check steps.
Address Verification: Ensure the "home office" matches the tax and legal requirements for the role.
Process Over Paranoia
The secret to fraud detection isn't being "tougher"—it's being consistent. When you have a standardized process, anomalies stand out automatically.
At Tenzo, we believe the hiring experience should be frictionless for honest candidates and impossible for fake ones. By weaving identity signals and consistency checks directly into your recruiting workflow, you stop fraud before it reaches your hiring managers—without slowing down your growth.
Ready to secure your hiring funnel?
Stop guessing and start verifying. Book a Tenzo demo today to see how we help high-growth teams automate candidate integrity.