Latest Blog
Fraud Prevention in Remote Hiring: Remote Hiring Fraud Controls for Identity, Device, and Remote Interview Security
Researcher
•
5 min read
Share this post
Fraud Prevention in Remote Hiring: Remote Hiring Fraud Controls for Identity, Device, and Remote Interview Security
Remote hiring scales teams fast. It also creates a new attack surface.
"Remote hiring fraud" is no longer limited to fake resumes. It can include identity misrepresentation, proxy interviews, AI-assisted cheating, location spoofing, payroll diversion, and coordinated attempts to get hired for access.
This article gives you a modern fraud-prevention stack for distributed teams. It is practical, layered, and designed to preserve candidate experience.
Table of contents
What remote hiring fraud looks like today
A threat model for remote hiring
The modern fraud-prevention stack
Remote interview security and interview integrity
Device and location verification signals
Escalation rules your team can actually run
Onboarding and first-access controls
Where Tenzo fits
Quick-start checklist
FAQ
What remote hiring fraud looks like today
Most incidents fall into a few patterns.
Identity substitution
The person who applies is not the person who interviews. Or the person who interviews is not the person who onboards.
Interview manipulation
A candidate receives real-time help from another person, from a second device, or from an AI assistant that rewrites answers and generates code or explanations on the fly.
Location spoofing
The candidate claims to be in one place, while their network, device, or behavior strongly suggests another. In high-trust roles, geography can become a security requirement, not just a recruiting detail.
Onboarding diversion
Banking and payroll information changes through weak channels. Equipment is shipped to mismatched destinations. Accounts are created and accessed from unexpected networks.
The uncomfortable reality is that fraud often succeeds because processes assume good faith and because teams lack clear step-up rules.
A threat model for remote hiring
Before you add tools, define where fraud can happen in your funnel.
Stage 1: Apply
Risks:
synthetic or stolen identity details
resume laundering and credential inflation
bot-driven application floods
Controls:
verify email and phone control
detect disposable patterns and repeated structures
maintain identity continuity from the first touch
Stage 2: Screen
Risks:
proxy screens and scripted answers
location mismatch
Controls:
structured screening questions
consistency checks across answers and timelines
Stage 3: Interview
Risks:
proxy interviews
AI-assisted cheating
off-camera helpers
Controls:
remote interview security controls and integrity signals
evidence capture so anomalies can be reviewed
Stage 4: Offer and onboarding
Risks:
payroll diversion
identity drift
device and access abuse
Controls:
step-up identity verification for finalists
out-of-band confirmation for sensitive changes
Stage 5: First access
Risks:
data exfiltration
rapid privilege escalation
persistent access via tokens and forwarded accounts
Controls:
least privilege and staged access
device posture and location consistency
monitoring and fast offboarding playbooks
The modern fraud-prevention stack
A good fraud-prevention program is layered. Each layer catches a different failure mode.
Layer 1: Identity verification and identity continuity
You are not trying to "prove" a person once. You are trying to ensure the same person shows up across steps.
Low-friction controls for everyone
confirm the candidate controls their email and phone
keep communication channels consistent across the funnel
flag identity drift, such as changing names, changing contact details, or inconsistent work history timelines
Step-up identity verification for finalists and high-trust roles
a quick identity check that ties the candidate to a government ID and a live selfie or liveness step
a controlled workflow to store verification results
This is where many teams get the balance wrong. Heavy checks at the top of funnel hurt conversion and do not stop serious actors. A step-up approach preserves experience while protecting the highest-risk boundary.
Layer 2: Interview integrity and remote interview security
Remote interviews fail when they become easy to outsource or easy to assist.
Interview integrity controls that work
use structured questions that force lived detail and decision-making
ask for timelines, tradeoffs, and what changed based on feedback
require follow-ups that test comprehension, not memorization
Make cheating harder without acting accusatory
use consistent rubrics so rehearsed scripts have less leverage
capture transcripts and summaries so suspicious patterns are reviewable
apply cheating detection signals as a risk input, not a verdict
If your process can only detect cheating by "vibes," it will miss quiet fraud and create inconsistent decisions.
Layer 3: Device signals and behavioral patterns
Device and behavior signals are not about spying. They are about detecting patterns that do not match a normal candidate journey.
Signals that tend to be useful:
unusual velocity across steps
repeated fingerprints across multiple candidates
anomalies in response timing and session patterns
mismatches between claimed location and technical indicators
Use these as probabilistic inputs. A single signal should not reject a candidate. Multiple signals should trigger step-up verification.
Layer 4: Location verification
Location matters for compliance, tax, customer requirements, and security. It also matters for high-risk geographies.
A strong policy looks like this:
verify location consistency across sessions
treat repeated mismatch as a step-up trigger
require stronger verification for high-trust roles
Avoid blanket rules like "no VPN" because they will reject legitimate candidates. Instead, treat obfuscation indicators as risk multipliers.
Layer 5: Onboarding and first-access controls
Most damage occurs after hire, not during the interview.
Controls that reduce real loss:
staged access that expands over the first days and weeks
out-of-band confirmation for payroll changes
equipment shipping confirmation through controlled workflows
monitoring for unusual access patterns in the first 30 days
If you only secure the interview, you are protecting the wrong boundary.
Escalation rules your team can actually run
The difference between "security theater" and real security is operational clarity.
Use three risk tiers
Tier 1: proceed
signals consistent
interview integrity normal
Tier 2: step up
one or two anomalies
examples: location mismatch plus unusually scripted answers, or inconsistent contact patterns
Tier 3: pause and investigate
multiple anomalies or strong indicators of deception
examples: identity drift, repeated evidence of outside assistance, repeated device reuse across accounts
A step-up menu that preserves candidate experience
Start with the least friction that resolves doubt.
live callback to the verified number
a short follow-up interview with a second interviewer
identity verification for finalists
a work sample designed to be hard to outsource in real time
for the highest-trust roles, a proctored or in-person final verification option
This keeps most candidates on the fast path while creating a reliable process for the edge cases.
Onboarding playbooks that prevent costly mistakes
Hiring fraud often becomes a security incident because onboarding is permissive.
Set your default access posture
least privilege on day one
staged access expansions tied to milestones
stricter controls for roles with admin rights, customer data, or financial systems
Protect payroll and high-impact changes
require out-of-band confirmation for bank changes
log approvals and changes in a single system
Make fast offboarding a first-class workflow
document device recovery steps
define who can disable accounts and revoke tokens
run a tabletop exercise so your team can execute under pressure
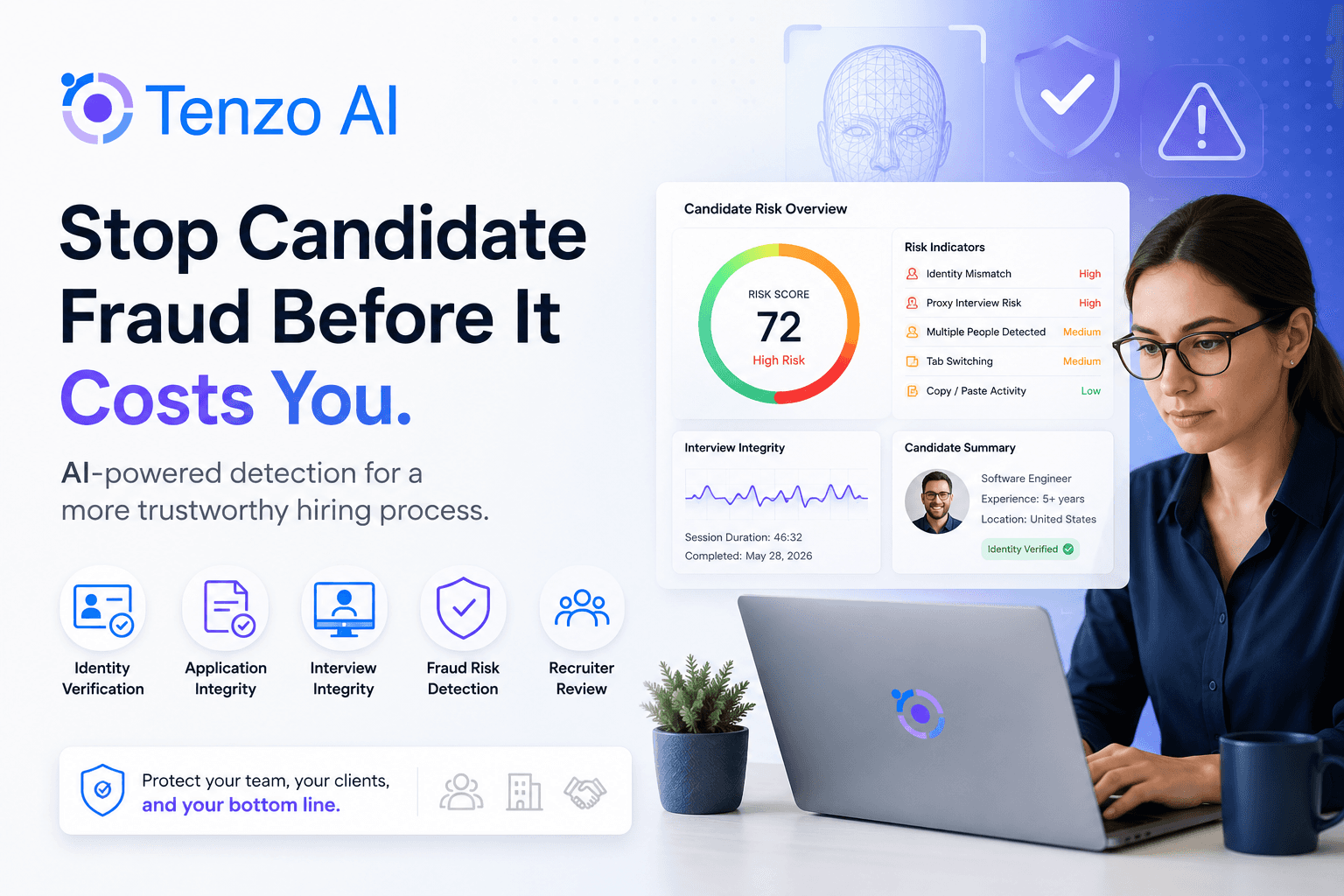
Where Tenzo fits in a modern fraud-prevention stack
Many teams adopt Tenzo because it strengthens the part of the funnel that is easiest to manipulate in remote hiring: the interview layer.
Tenzo can support a layered approach that includes:
identity verification for candidates, including quick "hold up your ID" checks to maintain identity continuity
interview integrity signals that help detect AI-assisted cheating and patterns consistent with off-camera help
location verification signals to confirm candidates are where they say they are and to trigger step-up checks when location is inconsistent
a broad set of additional fraud signals across the funnel, including email, phone, and resume monitoring indicators, plus many more
structured interviews and consistent rubrics that reduce the value of rehearsed scripts and create artifacts you can review and audit
If you want a practical workflow for your roles, Tenzo can map a step-up policy to your funnel and show you what checks to apply at each stage. Book a demo or consultation here.
Quick-start checklist: remote hiring fraud prevention
Use this as your baseline.
Identity
verify email and phone control
maintain identity continuity across steps
step-up identity verification for finalists in high-trust roles
Remote interview security
structured interviews and rubrics
evidence capture, such as transcripts, summaries, and scoring
step-up follow-ups when integrity signals appear
Device and location
track device and behavior signals as advisory inputs
verify location consistency across sessions
require step-up checks when mismatch repeats
Onboarding and access
staged access for the first week
out-of-band confirmation for payroll changes
fast offboarding playbook ready
FAQ
What is the most common form of remote hiring fraud?
Identity substitution and interview manipulation are the most common patterns. Either the person is not who they claim to be, or the interview reflects outside help instead of ability.
How do you prevent proxy interviews?
Use identity continuity checks for finalists, structured interviews with follow-ups that require real context, and step-up verification when multiple signals look off.
How do you detect AI-assisted cheating during interviews?
Combine structure with integrity signals. Structured questions reduce the value of generated answers. Signals can identify patterns consistent with real-time assistance. When signals appear, step up verification or run a follow-up evaluation.
Should you block VPNs?
No. VPN use can be legitimate. Treat it as a risk multiplier and focus on repeated inconsistencies across sessions.
When should you require identity verification?
Finalists, especially for high-trust roles, and any time multiple risk signals appear. The goal is identity continuity, not blanket friction.